The New Straits Times : Tech & U
Local coders graduate from Google stint
Date: 8th December 2008
Oriental Daily : Education(Page 4-5)

Page 4

Page 5
.
A blog on my random rants










-edited.jpg)




Changes since 0.7RC2
-Distinction made between Sony Ericsson,
Sony Entertainment & Sony Corp
(ex:the PS3 is distinguished and mapped accordingly)
-New manufacturers added to the detection scheme
*Blaupunkt
*Cisco
*Apple
*Microsoft
*Intel
*DoCoMo
*Samsung
UmitBT is a GUI based Bluetooth device scanner which does manufacturer detection. With UmitBT, not only are you able to probe for Bluetooth enabled devices, but also perform Service Discovery scans and identify the device based on the manufacturer of the device. The devices are then mapped out graphically based on the devices manufacturer.UmitBT is a branch of Umit and a product of GSoC 2008.















* Integrated Windows Installer
* Experimental Bluetooth Stack installer provided
* Vulnerability Scanner plugin (v0.6) integrated
* Several bugfixes

1. The beta version of the Neural Network optimized OS detection plugin(non-windows). Zaid's has a blog post about his achievement here.
2. The beta version of OSVDB based vulnerability scanner plugin
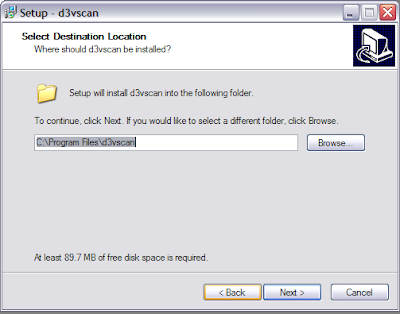
3. A unified Windows installer for d3vscan. Installing d3vscan on Windows would merely be a few mouse clicks away. Ondrej played a big role in this.
4. A Gentoo ebuild for d3vscan will be on the portage tree by next week.
5. Several d3vscan bugfixes.






d3vscan Alpha 7 release highlights:
-Bluetooth Map View
-Real-time SDP browse





Alpha 5.0 release highlights
-List View for both Bluetooth and Network mode.
-Able to parse Nmap's *.xml with multiple IP's
-Bluetooth mode uses Umit Light's native UBP file format.
-Bluetooth device manufacturer detection



Alpha 3.0 release highlights
-Able to load and save scans.
*Network mode uses Nmap's XML output.
*Bluetooth mode uses Umit's UBP file format.
(scheduled for Alpha 4.0)
-Preference and Plugin dialog added.
*Ability to customize Nmap scan flags
*Plugins framework.

"PortBunny is a Linux-kernel-based port-scanner created by Recurity Labs. Its aim is to provide a reliable and fast TCP-SYN-port-scanner which performs sophisticated timing based on the use of so called "trigger"-packets. The port-scan is performed in 2 steps: First the scanner tries to find packets, to which the target responds ("triggers"). Second, the actual port-scan is performed. During the scan, the triggers, which were found in the first scanning-phase, are used to determine the optimal speed at which the target may be scanned."